2
World Bank Fast Payments Toolkit
Glossary of terms
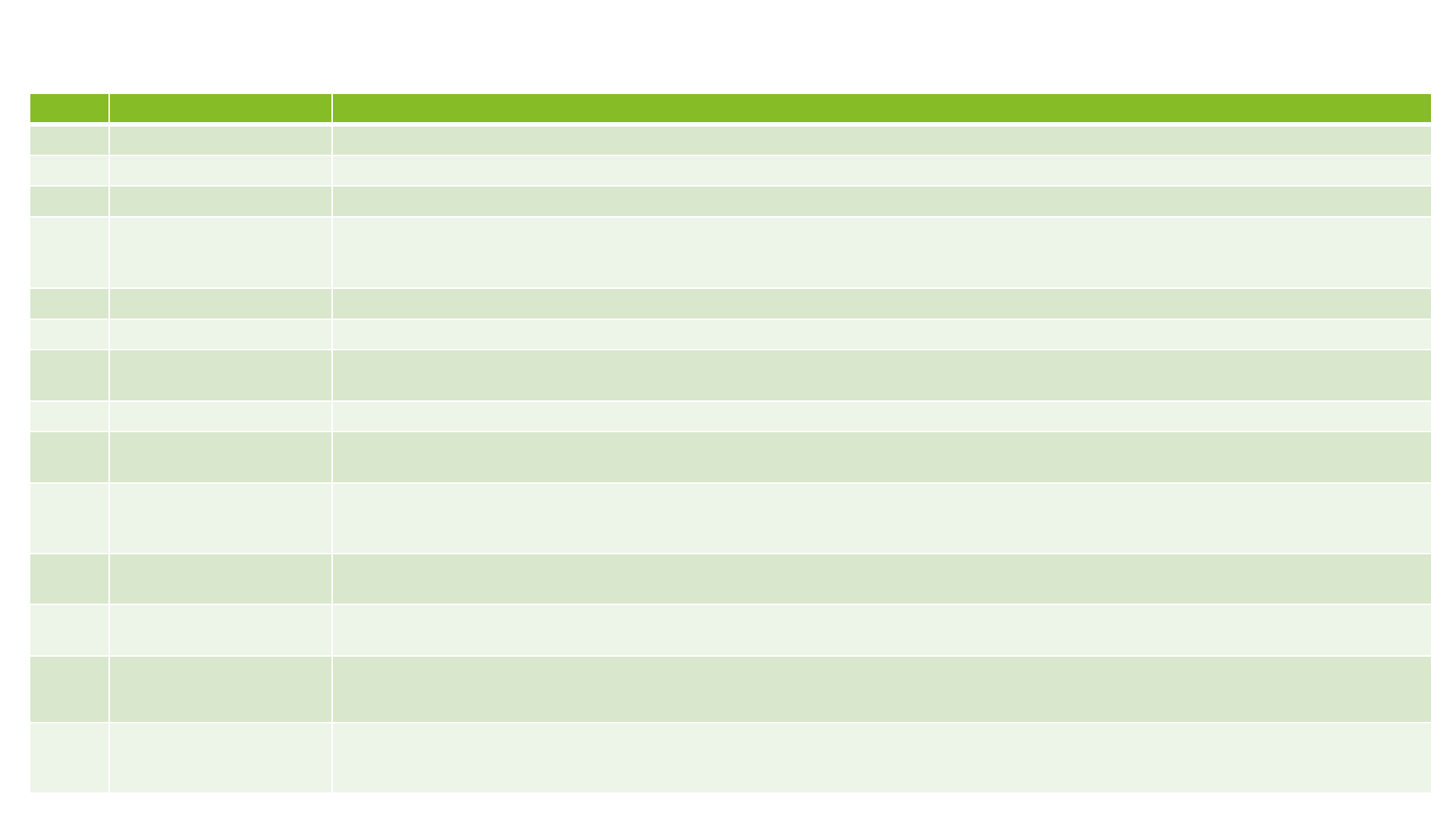
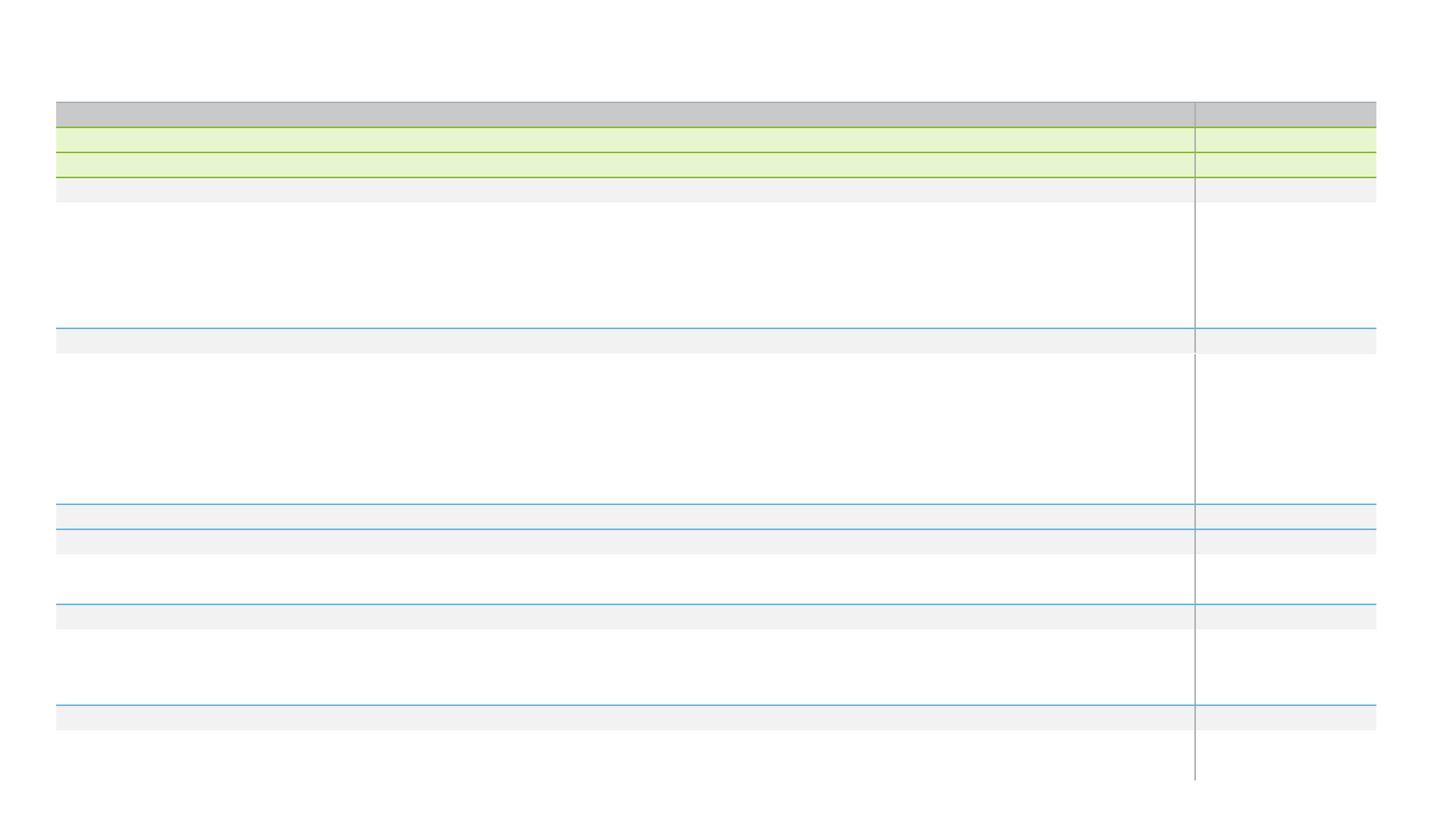
S. No. Term Definition
1 GDP Gross Domestic Product at current price
2 Income Category Classification as per World Bank based on Gross National Income (GNI) per capita
3 CPMI Committee on Payments and Market Infrastructure
4 FPS
As per CPMI, fast payment System is defined as payments in which the transmission of the payment message and the
availability of final funds to the payee occur in real time or near-real time and on as near to a 24-hour and 7-day (24/7) basis
as possible
5 Oversight Regulating or governing body supervising the payments system
6 Operator Institutions responsible for the operation of the payment system
7 Alias
Alternative to bank account numbers for increased convenience of the customer. For e.g., mobile number, national
identification number
8 Access Channels Modes used by customer to initiate transaction on FPS. For e.g., branch, internet, mobile
9
Individual Payment
Type
Person to person (P2P) – Payment between individuals for non-business purposes
10
Business Payment
Type
Person to Business (P2B) – Payment from an individual to a business entity
Business to Person (B2P) – Payment from a business entity to an individual
Business to Business (B2B) – Payment between two business entities
11
Government
Payment Type
Person/Business to Government (P/B2G) – Payment from person/Business to a government institution
Government to Person/Business (G2P/B) – Payment from government institution to a person or business entity
12 Credit transfers
Credit transfers are payment instruments based on payment orders or possibly sequences of payment orders made for the
purpose of placing funds at the disposal of the payee
13 Direct Debits
Direct debits are payment instruments in which the transaction is pre-authorized, and funds are blocked in account for a debit
to be initiated at a future date. In direct debits, payer’s account is debited on execution of mandate by merchant or payee
14 E-money
E-money is a prepaid value stored electronically, which represents a liability of the e-money issuer (a bank, an e-money
institution or any other entity authorized or allowed to issue e-money in the local jurisdiction), and which is denominated in a
currency backed by an authority
3
World Bank Fast Payments Toolkit
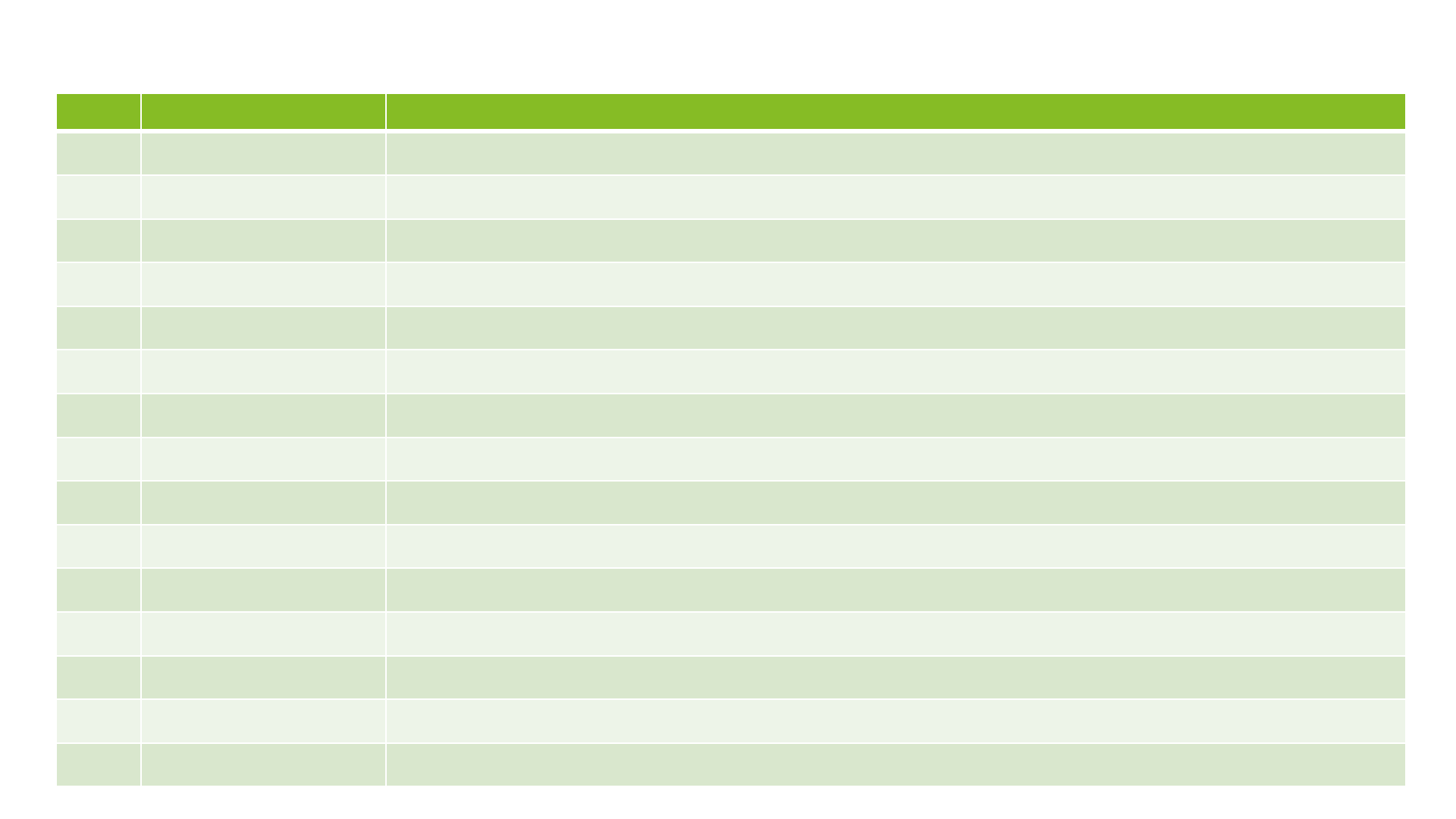
S.No. Term Expanded form
1 ABA American Bankers Association
2 CUNA Credit Union National Association
3 ICBA Independent Community Bankers of America
4 FDIC Federal Deposit Insurance Corporation
5 FFIEC Federal Financial Institutions Examination Council
6 FRB Board of Governors of the Federal Reserve System
7 NACHA National Automated Clearing House Association
8 NAFCU National Association of Federally-Insured Credit Unions
9 OCC Office of the Comptroller of the Currency
10 RTGS Real-time Gross Settlement
11 RTP Real time Payments
12 SIFMU Systemically Important Financial Market Utility
13 TCH The Clearing House
14 TLS
Transport Layer Security
15 TPSP
Third Party Service Provider
Abbreviations
4
World Bank Fast Payments Toolkit
Select parameters
Source : World Bank – 2019, Income Category: World Bank – June 2019
Others – World Bank 2017
* For age >15 years
GDP
GDP – $21.42 trillion
Income Category
High
Population
328.23 million
Access to mobile phone*
94.86%
Access to internet*
90.40%
Bank account*
93.12%
Branches per 100,000
adult
31.46
Made or received digital
payment in last 1 year*
91.10%
Received government wages
or transfer in account*
64.98%
5
World Bank Fast Payments Toolkit
How to read this report
• This deep dive report relates to the RTP system in USA
• It has been developed based on primary interviews with key stakeholders such as regulators, operators and participants in the
system as well as by leveraging secondary sources
• Key secondary sources include TCH website and RTP playbooks
• The table below presents a legend to assist readers as they navigate through different sections of the report
Legend
The green box with the adjacent icon indicates section/sub-section summary across the report. Reader may choose to
read through this for a high-level overview on the selected topic
The first slide of every section includes a chapter summary to provide readers with an overview of the section contents
6
World Bank Fast Payments Toolkit
Table of Contents
Slide number
A.
Executive Summary
8
B.
Detailed Report
1 Overview
1.1.
Background and Objectives | RTP 11
1.2.
System Development | RTP 12
1.3.
Key Milestones | RTP 13
1.4.
Background and Objectives | FedNow 14
1.5.
System Development | FedNow 15
2
Business and Operating Model
2.1.
FPS Structure 17
2.2.
Participants 18-20
2.3.
Payment Instruments and Payment Types 21
2.4.
Access Channels, Agent Network and Aliases 22
2.5.
Scheme Pricing and Fee Structure 23
2.6.
Use Cases / Services
24
3
User Adoption
25
4
Technical Details and Payment Process
4.1.
Technical Details (Messaging Format, QR Codes, APIs and Customer Authentication) 27-28
4.2.
Payment Process (Customer Registration, Transaction Fulfilment, Liquidity Management and Settlement) 29-32
5
Governance Framework
5.1.
Legal and Regulatory Aspects 35-36
5.2.
Risk Management 37-39
5.3.
Dispute Resolution and Customer Complaints 40
6 Annexure
6.1.
Key Features 42

A. Executive Summary
8
World Bank Fast Payments Toolkit
RTP | USA FPS
• RTP is a real-time electronic fund transfer system operating on 24*7 basis. It was
launched in November 2017
• The Clearing House (TCH) is the owner and operator of RTP. TCH Supervisory Board
and TCH Managing Board have appointed RTP Business Committee to oversee and
govern the system
• RTP’s development was primarily a market driven initiative. In 2014, TCH announced
Future Payments Initiative, this initiative paved the way for system development. RTP
enables consumers, businesses and government agencies to make real-time payments
in American Dollars
• TCH collaborated with Vocalink for the system development. The implementation of
the RTP network took approximately 30 months
Key features of RTP system are:
• Users can make RTP payments via traditional and alternate delivery channels
(Branch, ATM, internet or mobile banking platforms)
• Currently, the RTP system supports use cases/services like Bulk/Batch payments,
Bill Payments, Merchant Payments, Request to Pay and Recurring Payments
• TCH is currently collaborating with participating institutions to promote the usage of
bill payments. US Faster Payments Council has a working group that is looking at the
possibility of enabling QR payments using real time payments, including the RTP
network
• Real time payments
• Separation of technical
connection and settlement
mechanism
• Operates 24x7x365
• ISO 20022 messaging
standard
• Real time gross settlement
• Fraud detection services
Source: TCH | Primary Interviews

B. Detailed Report
10
World Bank Fast Payments Toolkit
1. Overview
Chapter Summary:
• Future Payments Initiative was announced in 2014 by The Clearing House that paved
the way for development of RTP system
• The guiding principles of RTP system include Ubiquity, Adaptability, Extensibility and
Global Compatibility
• RTP system was a market driven initiative as TCH worked closely with industry associations
to develop a system that would fulfil payment needs in an increasingly digital economy
• TCH partnered with Vocalink for system development. It took approximately 12 months
to assess business requirements and 18 months to develop RTP system and on-board
initial six participants
• RTP system core infrastructure is based on Vocalinks’s Instant Payment Service and
resembles the basic architecture used in the FPS in Singapore and Thailand
• Access model for RTP system has been customized to meet the requirements of the USA
market. It separates technical connection and settlement mechanism and allows
several approaches to participants for connecting with the system
Chapter sections:
1.1. Background & Objectives
1.2. System Development
1.3. Key Timelines
Source: TCH | Primary Interviews
11
World Bank Fast Payments Toolkit
1.1. Background and Objectives | RTP
RTP system is the first new core payments infrastructure in the USA in the last 40 years. It was launched by The Clearing House (TCH) in
November 2017. RTP is a real time, 24*7 payment and messaging system that allows immediate fund transfers through accounts at financial
institutions. The Clearing House, payments consortium of 25 banks and various technology companies, is the owner and operator of the RTP
system.
RTP system was built for financial institutions of all sizes and serves as a platform for innovation allowing financial institutions to deliver new
products and services to their customers. Financial Institutions can integrate into the RTP network directly, through Third-Party Service
Providers, Bankers’ Banks and Corporate Credit Unions.
• The Clearing House
launched the RTP
network in
November 2017 to
bring real-time
payments to the
USA
• RTP system was a
market driven
initiative as TCH
worked closely with
industry association
to identify consumer
and business cases
with need for the
real time payments
• The guiding
principles of RTP
system include
Ubiquity,
Adaptability,
Extensibility and
Global
Compatibility
In 2014, The Clearing House launched its Future Payments Initiative based on the recommendations from its supervisory board, which
consists of several industry leaders from financial institutions. The aim of this initiative was to develop a strategic view of RTP based on an
extensive study of payment needs in an increasingly digital economy. Through this review, TCH assessed several aspects surrounding RTP:
• TCH worked closely with industry associations including the Federal Reserve, NACHA, ABA, ICBA, NAFCU, CUNA and TCH banks to
identify consumer and business cases with the greatest need for RTP that represent the best incremental value for customers
• The Future Payments initiative considered the experience and lessons learnt from other countries who had already established
their own real-time payments system
• TCH also reviewed ways in which a potential RTP system for the U.S. could maintain and improve the safety and soundness of existing
payment systems
RTP system was a market driven initiative as TCH worked closely with industry associations to develop a
system that would fulfil payment needs in an increasingly digital economy
Source: TCH | Primary Interviews
TCH has developed a safe, sustainable, standards-based RTP system that is inclusive of all the financial institutions (FIs) in the USA. RTP
system includes extensible messaging and robust security and allows FIs to develop creative and innovative products for their customers.
The guiding principles followed by TCH for development of the system include the following:
Ubiquity – Accessible to FIs of all sizes and charter
types in order to reach the vast majority of U.S. account
holders
Extensibility – Rich, flexible messaging functionality to
support innovative value-added products
Adaptability – Able to adapt as expectations and risk
environment inevitably change over time
Global Compatibility – Use of international global
standards to facilitate future interoperability & to ease
the implementation burden for multinational FIs
12
World Bank Fast Payments Toolkit
1.2. System Development | RTP
Based on the findings from Future Payments Initiative, TCH announced a multiyear initiative to build a ubiquitous RTP system for the
USA. Faster payments Task Force was formed to identify and assess approaches for implementing safe, ubiquitous, faster payments
capabilities in the USA. TCH had submitted the design of the RTP system for an independent evaluation. RTP's proposed design met all
the 36 assessment criteria identified by the task force.
Infrastructure Setup – Key decisions
• RTP system resembles the basic architecture used in the FPS in Singapore and Thailand. However, it has undergone extensive
modifications to meet the local market requirements in particular settlement mechanism, access model and non-payment messages
(request to pay, request to confirmation, etc.)
• Access model separates technical connection and settlement mechanism. This model was adopted keeping in mind the complexity of USA
market. It allows all the financial institutions to connect with the using several approaches
• Network connectivity is via MPLS or Secure VPN. In addition to the security provided by the MPLS or Secure VPN connection, MQ
Transport Layer Security (TLS) is utilized and each message is digitally signed to ensure authenticity in accordance with ISO 20022
• Real time gross settlement (RTGS) mechanism was chosen for final settlement for ensuring the settlement finality
•
The Clearing House partnered with Vocalink for the development
of RTP system
•
An RFP was issued for vendor selection for which TCH received
response from 3 service providers. After the selection process laid out
by TCH, Vocalink was on-boarded for system development in
December 2015
•
As development of the RTP system was a market driven initiative, the
system development cost has been paid by the financial institutions
owning The Clearing House
Development Process Implementation Timelines
• TCH announced the
development of the
RTP system based
on findings from its
Future Payments
Initiative
• Vocalink was on-
boarded for
development of RTP
system after a
vendor selection
process
• System development
timelines were
approximately 30
months as RTP was
launched in
November 2017
Development
Cost
• Technical costs involved in the
system development were not high
though cost of deployment for
participant was significant ranging up
to $2 billion
Development
Timelines
• 12 months defining the requirement
of the system in collaboration with
market participants
• 12 months for system development
and 6 months for testing and on
boarding initial six participants
Source: TCH | Primary Interviews
13
World Bank Fast Payments Toolkit
1.3. Key Milestones | RTP
TCH launched
its Future
Payments
Initiative
Vocalink
was on
boarded for
the system
development
Note: Above list is not exhaustive
With its launch in 2017, RTP is a relatively new system. There is a scope of several milestones as the system progresses ahead in its lifecycle journey
2014 2015
2017
2018 2019
RTP was
launched in
November
2017
TCH forms an
RTP Advisory
Committee to
gather additional
input
FirstBank
joins the RTP
network
Wells Fargo
declares it will
offer RTP to
corporate
customers
2016
Source: TCH | News Articles
14
World Bank Fast Payments Toolkit
1.4. Background and Objectives | FedNow
Federal Reserve announced on August 5
th
, 2019, that it will build and operate a real-time payments system called FedNow. Key drivers
for development of the FedNow are prevailing market conditions as well as future market outlook. Federal Reserve also worked on policy
considerations in case of its involvement in real time payments. Policy considerations by Federal Reserve are as follows:
• System should recover cost in the long run
• Service has to provide clear public benefit
• Service should be one that other providers alone cannot be expected to provide with reasonable effectiveness, scope, and equity
While there weren’t RTP specific gaps which prompted development of FedNow, the Federal Reserve Board’s assessment determined that in
case there would only be a single fast payments solution in the USA, it would face significant challenges, including achieving nationwide
reach.
• Federal Reserve
worked on policy
considerations for
its involvement in
real time payments.
Federal Reserve
Board’s assessment
determined that a
single FPS solution
in the USA would
face significant
challenges, including
achieving nationwide
reach.
• The key drivers for
development of
FedNow were
Accessibility,
Safety and
Efficiency
Objectives
FedNow
Accessibility: Federal Reserve looked at accessibility to real time payments in case it operates the fast payments settlement service.
There are 10k+ financial institutions in the USA, which are quite diverse in terms of geography, size and type of customers served.
FedNow would be accessible by all these financial institutions and hence would provide nationwide reach
Safety: Having an additional fast payments settlement service in addition to RTP would ensure resiliency in case one service faces any
crisis situations. Also, as the Federal Reserve is the Central Bank, it would be able to provide liquidity and continuity in case of any
crisis or natural disasters
Efficiency: With FedNow as the core infrastructure, other financial institutions would be able to build modern and innovative service on
top of this infrastructure. Having another fast payments settlement service would also provide a healthy competition just like other
payment services operating in the USA. This would also ensure reduced pricing and enhanced service quality.
Source: Primary Interviews
FedNow service is intended to be a platform which would enable FIs to develop innovative use cases / services. This service is primarily
meant to facilitate real time interbank settlement. FedNow would also enable certain use cases / services based on input received from the
industry participants. For example: Request to Pay service to enable convenient online bill payments, etc. Over time, participants and their
partners would develop the uses cases/services desired by the end users. Federal Reserve will work with participants to supplement those
service.
15
World Bank Fast Payments Toolkit
1.5. System Development | FedNow
Source: Primary Interviews
• The Federal Reserve carried out public benefit analysis and put out a
public notice for comments on features and functionality that this
service should have. Based on the feedback from this public notice,
the Federal Reserve will develop functionality of the FedNow system
• Going forward, the Federal Reserve has also constituted the FedNow
community consisting of stakeholders from private sector to provide
insights and inputs for the development of FedNow
Infrastructure Setup
• FedNow is expected to go live by 2023 or 2024
• Before the launch of the system, pilot testing will be conducted with
FIs. The detailed timelines will be put in place by Federal Reseve
Implementation Timelines
• FedNow would be a completely new system. Settlement mechanism
would be based on credit and debit of master accounts held by FIs
with the Federal Reserve. FedNow is currently scheduled to be
launched in 2023 or 2024.
• The Federal Rerserve has requested information and currently in
process of examining the proposals sent by the vendors. Meanwhile,
Federal Reserve has completed drafting of ISO message flows,
specifications for industry feedback, established FedNow community
and drafted business requirements for the system
Development Process
• The Federal Reserve is open to exploring the message exchange
model in the future but that is the one that would require
participation by TCH. The initial launch of the FedNow service will be
intended to facilitate routing interoperability
• The Federal Reserve is committed to working towards compatible
standards and operating procedures with the existing private-sector
service, which will enable interoperability through the model of
payment routing, and has initiated discussions on this subject with
the existing private-sector service toward that end
Interoperability
16
World Bank Fast Payments Toolkit
2. Business and Operating Model
Chapter Summary:
• TCH is the owner and operator of RTP system. RTP Business Committee has been
appointed for overseeing the system activities
• RTP allows every federally insured depository institution in the USA to become a
participant in the system. These institutions can connect with the system directly or
through a third-party service provider (TPSP)
• RTP enables consumers, businesses and government agencies in the USA to make
payments in American Dollars between accounts, e-wallets of the participating financial
institutions
• RTP doesn’t support aliases for completion of payments on its core infrastructure, though
third-party PSPs can enable aliases through their application for the end users
• RTP supports form-factor neutrality and allows transactions across both traditional and
alternate delivery channels
• Agent networks (assisted mode of transfer) are not supported in RTP network
• RTP system follows same pricing structure for all participants with no volume discounts,
no volume commitments and no monthly minimums to ensure that financial institutions of
all sizes participate on the same terms
• RTP Participants are free to decide on charges levied to end users
• RTP supports multiple use cases/services like Request to Pay, Merchant Payments,
Bill Payments, Bulk/Batch Payments and Standing Orders
Chapter sections:
2.1. FPS Structure
2.2. Participants
2.3. Payment Instruments and Payment Types
2.4. Aliases, Access Channels & Agent Networks
2.5 Scheme Pricing and Fee Structure
2.6 Use Cases/Services
Source: TCH | Primary Interviews
17
World Bank Fast Payments Toolkit
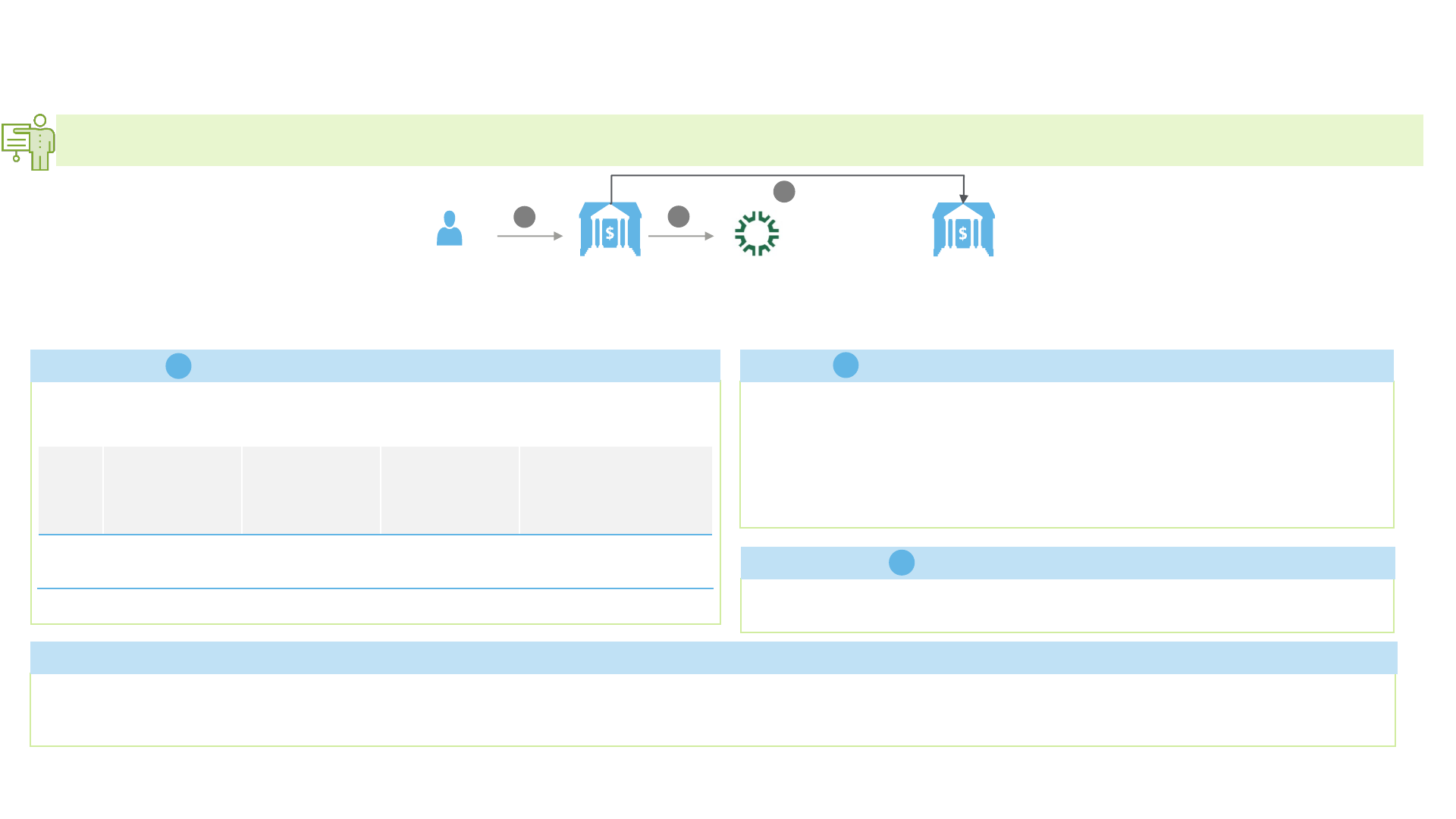
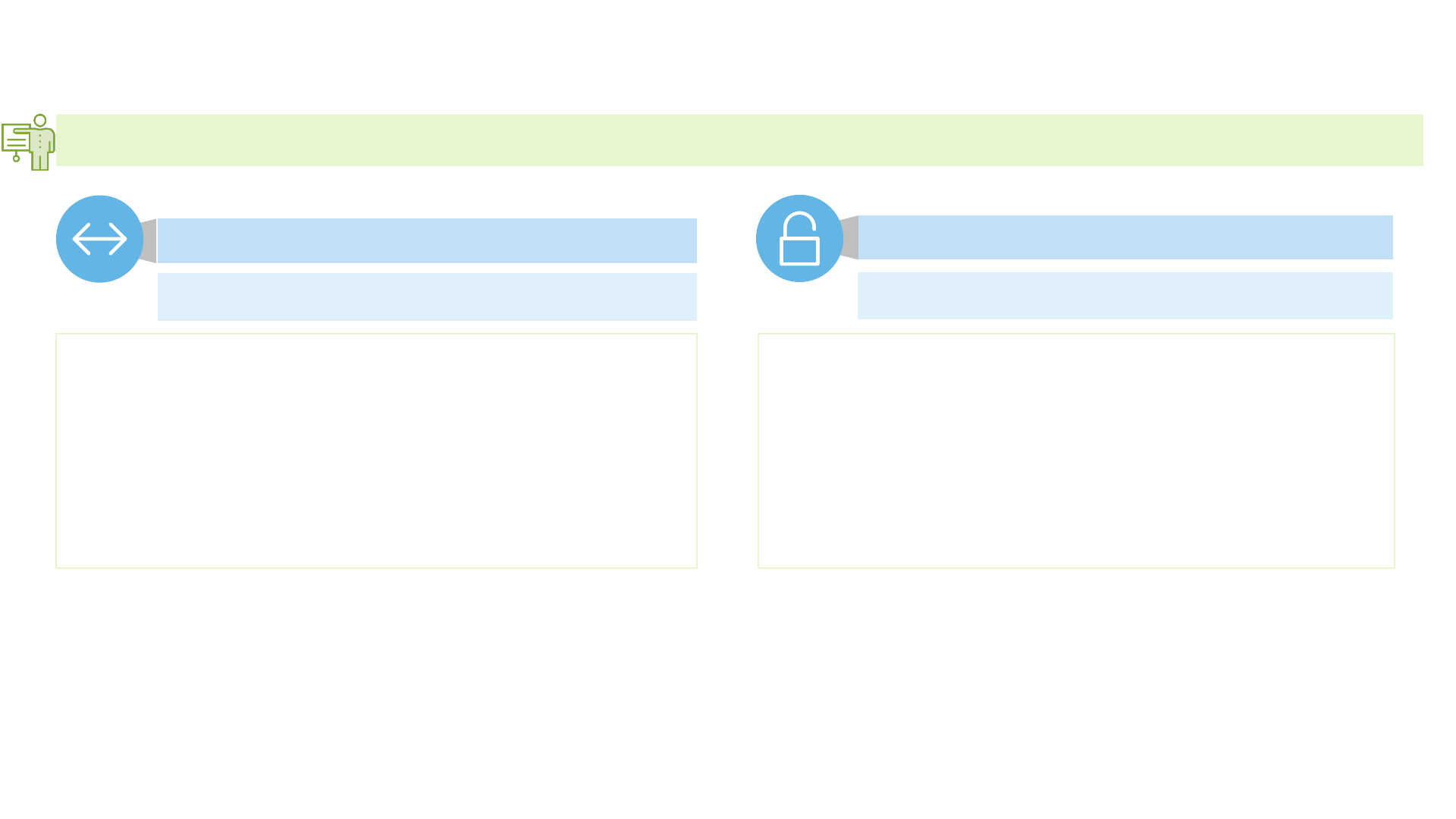
2.1. FPS Structure
• The Clearing House
(TCH) is the owner
operator and
overseer of RTP
system.
• TCH is owned by the
consortium of
commercial banks
and technology
companies in the
USA and is
responsible for
overseeing the day-
to-day operations
and maintenance of
the system
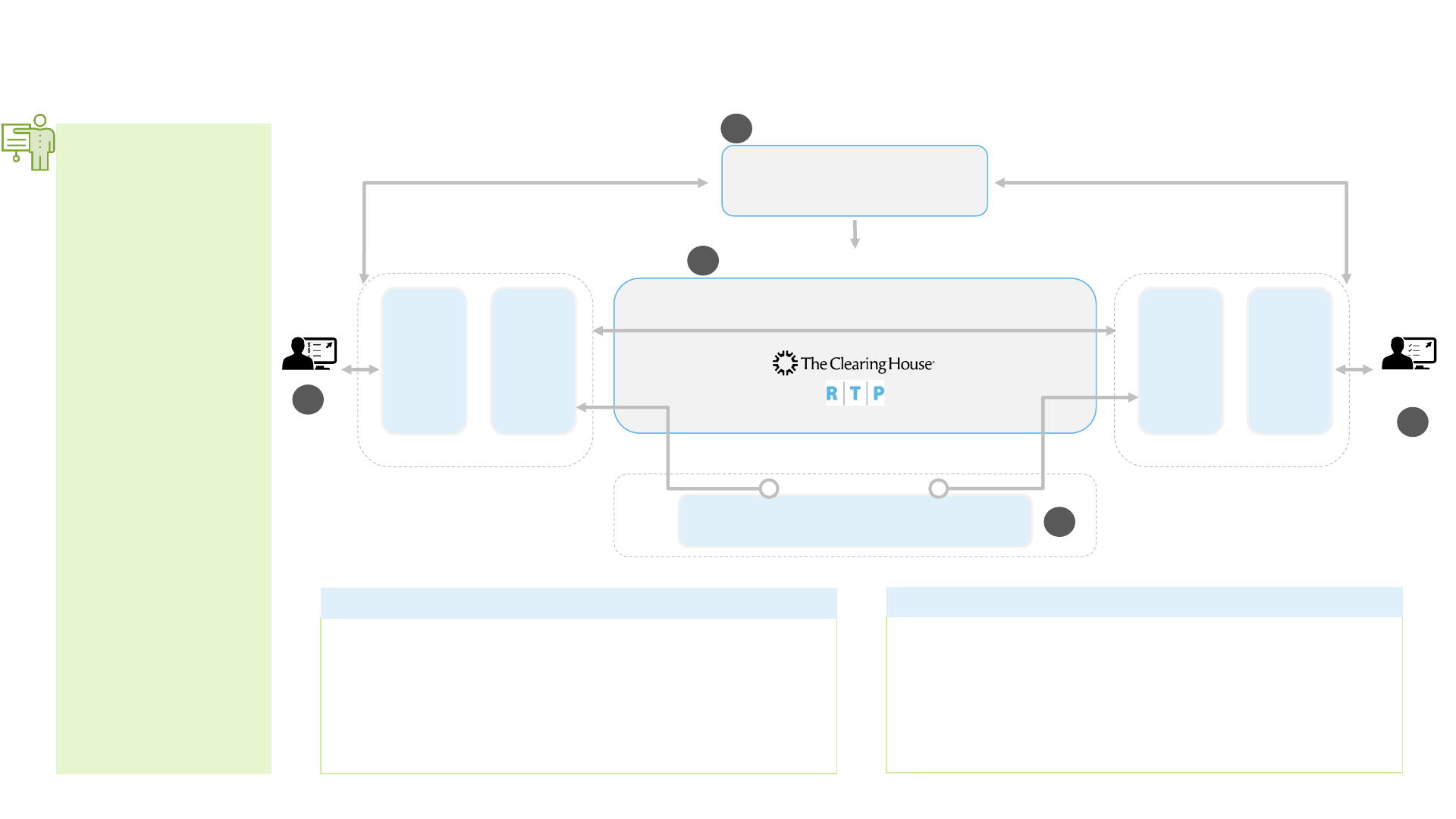
Sending
Customer
Receiving
Customer
Bank
Channels
Payment
Gateways
RTR Participants
Overlay Services
Payment
Gateway
Bank
Channels
RTR Participants
Payment Exchange
& Notification
Settlement
Request
& Notification
Settlement
Notification
Interbank Clearing and Settlement Services
(Real-time settlement)
Real Time Rail Utility
i
ii
iii
iv
v
Additional
3
rd
-party
services
Source: TCH | Primary Interviews
• Board of Governors of the Federal Reserve System (FRB),
Office of the Comptroller of the Currency (OCC) and the
Federal Deposit Insurance Corporation (FDIC) jointly
regulate TCH and services provided by it.
• These institutions are not responsible for direct supervision
of RTP system. RTP Business committee is responsible to
govern the RTP system
• TCH is owned by consortium of commercial banks and
technology companies in the USA
• It is responsible for overseeing the day-to-day operations
and maintenance of the system
Regulators
The Clearing House (TCH)
18
World Bank Fast Payments Toolkit
2.2. Participants (1/3)
Requirements for Participants
• To become a direct participant in RTP system, financial institutions have to meet the
following requirements:
• Comply with the business and operating rules set by the TCH
• Undergo technical assessment
• Financial institutions connecting indirectly through TPSPs also have to undergo
certification process for connecting with the system
Membership Statistics
• As of November 2020, there are 63
participant banks and credit unions in
the RTP system
• Other service providers:
• 19 Third Party Service Providers (TPSPs)
• 4 funding agents
• RTP allows every
federally insured
depository
institutions in the
USA to connect with
the system. These
institutions can
either directly
connect with the
system or through
TPSPs
• Prospective
Participants need to
comply with the
business and
operating rules
and undergo
technical
assessment to
connect with the
system
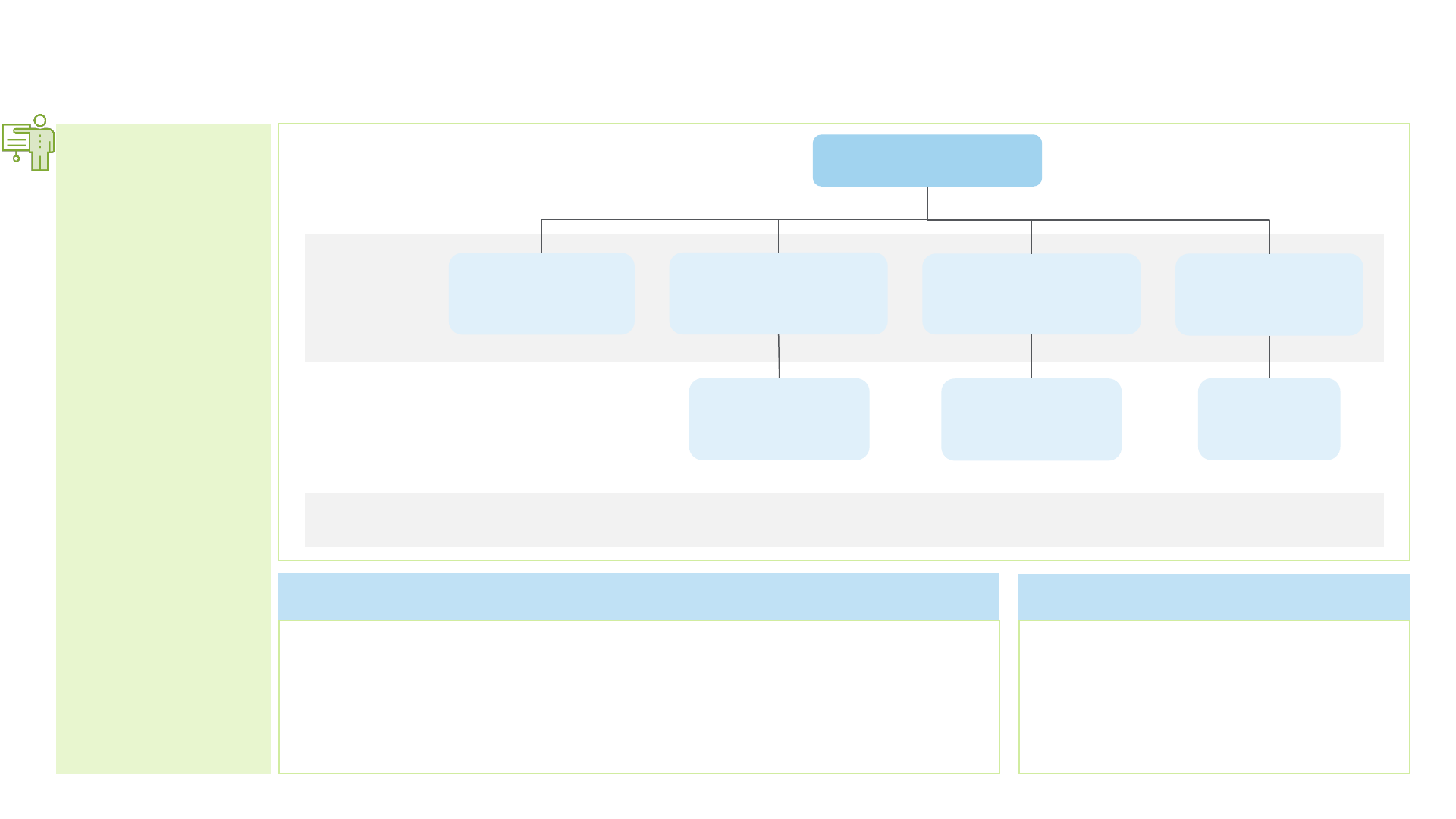
RTP
Financial
Institutions
Third Party Service
Providers (TPSPs)
Direct
Connection
Corporate Credit
Unions
Bankers Banks
Financial
Institutions
Credit Unions
Community
Banks
Participants can connect as either funding participants or non-funding participants. Non-funding participants have to appoint funding
providers or funding manager to fulfil their settlement obligations.
Source: TCH | Primary Interviews
Indirect
Connection
19
World Bank Fast Payments Toolkit
2.2. Participants (2/3)
• There are four
participant
categories defined
as per RTP
participation rules –
Funding participant,
Non-Funding
Participant,
Receiving participant
and Sending
Participant
• Both financial
institutions and
TPSPs undergo
certification testing
to verify the
requirements for
handling both
payment and non-
payment message
Regulatory Considerations
Onboarding Process
Certification testing to verify the
technical requirements for handling
both payment and non-payment
message
Interoperability
TPSPs must also certify all the FIs
connecting through it or the core
banking solution (in case of large
TPSP)
Documentation (participants
must enter into a participation
agreement with TCH
For participation in RTP, interested
depository institution must communicate
intention to TCH
• Transfers between banks and non-
banks participants are allowed
Only a depository institution is eligible to become a Participant in the RTP System. These
institutions should have ability to connect with the system either directly or through a TPSP that
has been approved by TCH, in accordance with RTP Operating Rules and the RTP Technical
Specifications.
Bankers’ Banks and Corporate Credit Unions may provide connections to the RTP network as well
as liquidity management services for financial institutions that may not want to connect directly
to the RTP system.
There are four participant categories defined as per RTP participation rules:
• Funding participant: Funding participant becomes a party to the RTP Prefunded Balance
Account Agreement with the Prefunded Balance Account Bank Agreement and requests and
receives disbursements from the Prefunded Balance Account to its Federal Reserve account.
In case it is a sending participant, it is required to fulfil prefunding obligations. Funding
participant is required to
• Maintain a reserve or clearing account with a Federal Reserve Bank
• Be accepted as a funding participant by TCH and the prefunded balance account bank
• Non-funding participant: Non funding participant has to designate a Funding Agent to act
on its behalf to prefund in accordance with these RTP Participation Rules and the RTP
Operating Rules
• Receiving participant: Participant that holds the Receiver’s Account and that receives a
Payment Message
• Sending participant: Participant that holds the Sender’s Account and initiates a Payment
Message
A participant must be (i) either a funding participant or a non-funding participant, and (ii)
a receiving participant. A participant also may be a sending participant
Source: TCH | Primary Interviews
Connectivity
• Due to the high number of Financial
Institutions in the USA, ease of
connectivity is critical for all FIs. Using
TPSP’s technical connection, small FIs
that are able to connect with the
system through TPSPs. This
connectivity option was an added
incentive for smaller FIs to join.
20
World Bank Fast Payments Toolkit
2.2. Participants (3/3)
• TCH, funding
participants and
funding agents enter
into an agreement
with the Prefunded
Balance Account
Bank
• This joint
prefunded balance
account is used for
the purpose of
supporting the
operations of the
RTP System
• RTP Operating Rules
also establish
requirements for
Third-Party Service
Providers
Regulatory Considerations
RTP Prefunded Balance Account Agreement is an agreement that TCH, funding participants and funding agents enter into with the
Prefunded Balance Account Bank. The joint prefunded balance account is used for the purpose of supporting the operations of the RTP
System. According to this agreement:
• All the funds deposited in prefunded balance account are payable exclusively in accordance with the instructions of TCH, which acts as
agent on behalf of all funding participants and funding agents
• Prefunded Balance Account is only used in support of RTP activities. Participants and funding providers can maintain excess liquidity for
only in case of reasonably anticipated liquidity needs for their or their non-funding participants’ RTP Payments
• Funding agent become a party to the Prefunded Balance Account Agreement. It is either a Funding Manager (provides prefunded
requirement, supplemental funding and requests disbursements for its non-funding participant); or a Funding Provider (depository
institutions that have their own current prefunded position and provides funding for non-funding participants through it)
Source: TCH | Primary Interviews
Participants can designate a third-party service provider to act on its behalf as agent to send and receive transmissions of Payment
Messages, Payment Message Responses, and Non-payment Messages, using the TPSP’s technical connection.
Requirements for Third-Party Service Providers are:
• It must be designated by one or more Participants to act as a Third-Party Service Provider in accordance with procedures established by
TCH
• It must satisfy the applicable provisions of the RTP Information Security Standards and Requirements and the RTP Technical
Specifications, as certified by the Participant in accordance with procedures established by TCH
Use of Third-Party Service Providers
21
World Bank Fast Payments Toolkit
2.3. Payment Instruments and Payment Types
• RTP allows credit
transfer and e-
wallets as payment
instruments. Direct
Debits are not
supported for RTP
payments
• RTP enables
consumers,
businesses and
government
agencies in the
USA to make
payments in
American Dollar
between accounts of
the participating
depository
institutions
• Credit transfer limit
on the RTP network
is currently
$100,000
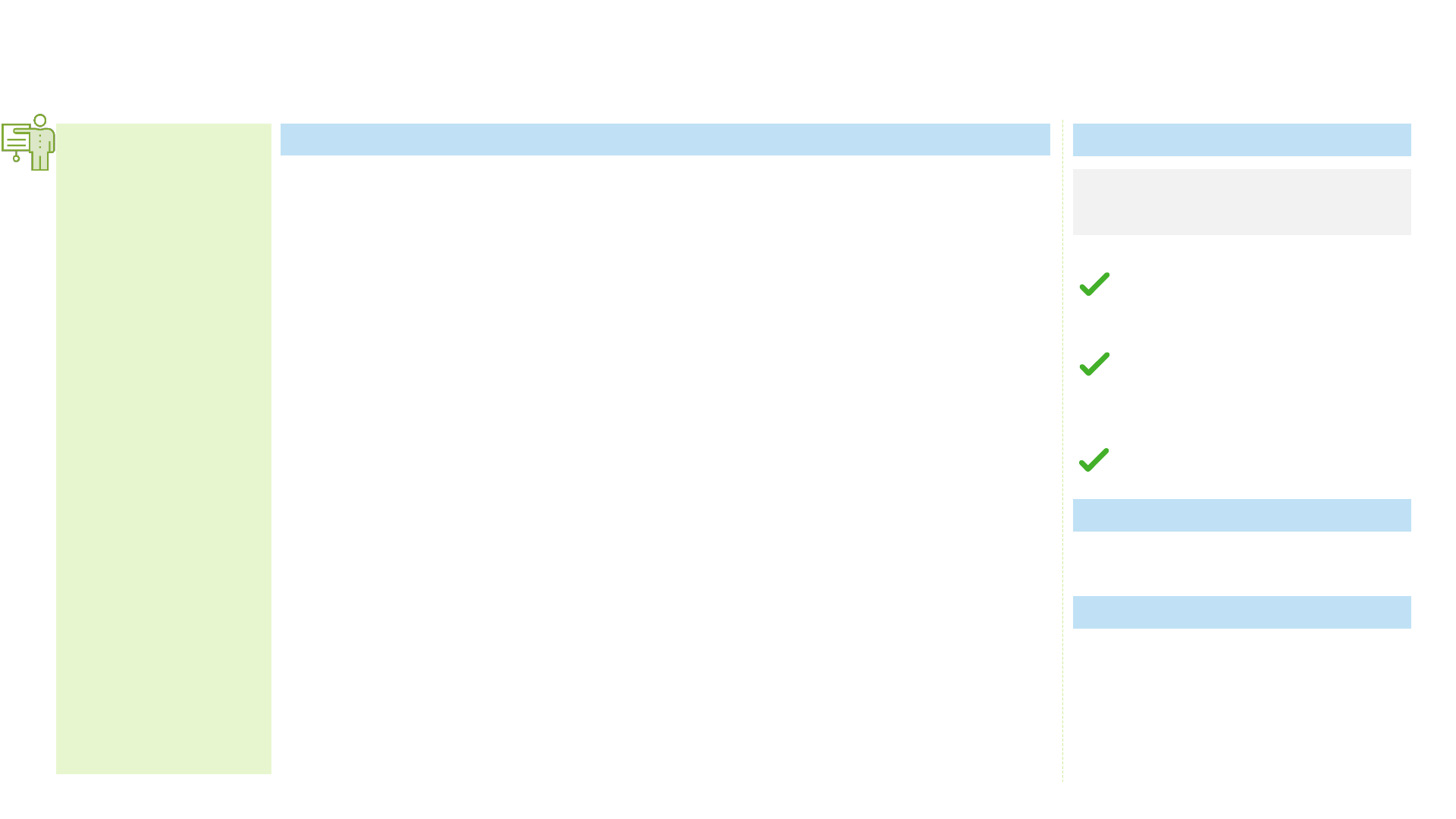
Payment Instruments Supported
• RTP supports credit transfer and e-wallets as payment instruments. TCH supports Venmo (which is a
wallet) to use RTP for instant money transfer to a consumer’s account
• Account to account interoperability is supported in RTP through credit transfer. The design principle
of RTP network is based on ‘Credit Push’ meaning that the customer authorizes the debit each time
Interoperability
Payment
Types
Individual
GovernmentBusiness
• Sending Participants are allowed to establish a lower transaction limit for
their senders. Receiving Participants are not allowed to establish a lower
transaction limit for their receivers
Credit transfer limit on the RTP network is currently $100,000
Transaction
Limit
Payment Types and Transaction Limit
✓
✓
✓
Transaction Currency
American
Dollar
(USD)
Credit Transfer
E-money
✓
✓
Direct Debit
Source: TCH | Primary Interviews
22
World Bank Fast Payments Toolkit
2.4. Aliases, Access Channels and Agent Networks
Aliases
• RTP system inherently doesn’t support use of aliases or proxies for
payments. Though the network allows third parties to enable alias or proxy
payments
• PayPal & Venmo currently use the RTP network for transfers to their clients
bank or credit union accounts using aliases. TCH has entered into partnerships
with payment service providers Zelle to provide settlement services. Currently,
integration of RTP and Zelle is under progress. Zelle allows use of mobile
number or email address as aliases
• There are no plans to launch RTP’s own social alias/proxy service because
the market is already well served and existing alias/proxy services might
transition to RTP payments to clear and settle transactions
• The RTP network will support tokenization of account numbers which could
be a way to allow payment originators and payment service providers to replace
account numbers with tokens that cannot be used to debit accounts, nullifying
the threat of data breach
• RTP supports form-factor neutrality and allows transactions
across both traditional and alternate delivery channels
• RTP network is core payment system and doesn’t deploy any
end user applications. It can support payments through
proximity-based channels. Though currently there are no end
user applications supporting payments through QR and NFC
• Agent networks (assisted mode of transfer) are not supported in
RTP system
RTP doesn’t have its own aliasing service though third-party application can enable use of aliases for RTP payments. RTP allows transactions though both
traditional and alternate delivery channels. It does not support payments through agent networks
Access channels and Agent Networks
Source: Primary Interviews
ATMBranch Mobile
Banking/Apps
Internet
Banking
23
World Bank Fast Payments Toolkit
RTP system follows same pricing structure for all participants with no volume discounts, no volume commitments and no monthly minimums to ensure that
financial institutions of all sizes participate on the same terms
2.5. Scheme Pricing and Fee Structure
The system participants are not required to pay joining fees while onboarding the
system. Participants pay only for the transactions they originate.
Network fees
1
Request for Payment Incentive Fee: Upon each successful RTP Credit Transfer
sent in response to a Request for Payment message, the participant that initiated
the Request for Payment owes the incentive fee to the participant initiating the
RTP credit Transfer.
TCH facilitates the collection and disbursement of Request for Payment Incentive
Fees between participants. TCH is not obligated to distribute incentive Fees that
TCH is unable to collect from the owing participant.
Fees owed to other participants
2
Each RTP Participant is free to decide the transaction charges levied to end
users
Fee charged to users/payee
3
User /
Payee
Sending
participant
The Clearing
House
1
2
3
Receiving
participant
Source: TCH | Primary Interviews
Credit
Transfer Sent
Request for
Payment
Sent
Remittance
Advice Sent
Prefunded Balance
Account Drawdown
Request Executed
Overall cost of connectivity associated with either the MPLS or secure VPN connections to the RTP network is calculated by The Clearing House and charged as pass through on
a monthly basis. Connectivity costs applies to any participant with a direct connection. In case of third-party service provider, connectivity fee is shared by financial
institutions connecting through it
Network-at-Cost Pass-through
24
World Bank Fast Payments Toolkit
2.6. Use Cases/Services
• RTP system supports ‘Request for Payment’, which
require a payer to authorize a payment in
response to the request
• In the payment message, the payer is provided
with the necessary pre-populated information
for the RTP payment
• This functionality provides payees with an
effective method to initiate a potential
transaction, while also combatting fraud and
allowing the payer to maintain control over the
payment flow
Access Channels
Payment Instruments
Credit transfer
Pricing Scheme
• No special charge
• Merchant Payments are supported as a use case
in RTP system
• Similar to Bill Payments, Request for Payment
acts as a complementary service to drive the
adoption of Merchant Payments
Access Channels
Payment Instruments
Credit transfer, E-money
Pricing Scheme
• No special charge
Mobile
• Bill payments are supported as a use case in RTP
system
• Request for Payment acts as a complementary
service to drive the adoption of Bill Payments
• TCH is collaborating with participant financial
institutions to further drive traction for this use
case
Access Channels
Payment Instruments
Credit transfer, E-money
Pricing Scheme
• No special charge
Mobile
Internet
RTP is a core payment system which has been designed to accommodate multiple use cases/services. TCH is focused on facilitating an able infrastructure
using which FIs can develop innovating use cases/services for end consumers
Request for Payment
Merchant Payments
• Bulk/Batch payments (e.g., payroll, etc.) are
supported in RTP system though it is processed in
form of individual credit transfer payments
• Participating financial institutions disaggregate the
bulk payments order and submit them in form of
series of individual RTP payments
Access Channels
Payment Instruments
Credit transfer
Pricing Scheme
• No special charge
Bill Payments
Bulk/Batch Payments
Internet
Mobile
Internet
• Recurring Payments or Standing Orders are
supported in RTP
• Users may have the option to set up a recurring
transaction with their respective FIs. Though user
have to authorize the payment at every instance
Access Channels
Payment Instruments
Credit transfer
Pricing Scheme
• No special charge
Recurring Payments
Mobile
Internet
Source: TCH | Primary Interviews
25
World Bank Fast Payments Toolkit
3. User Adoption
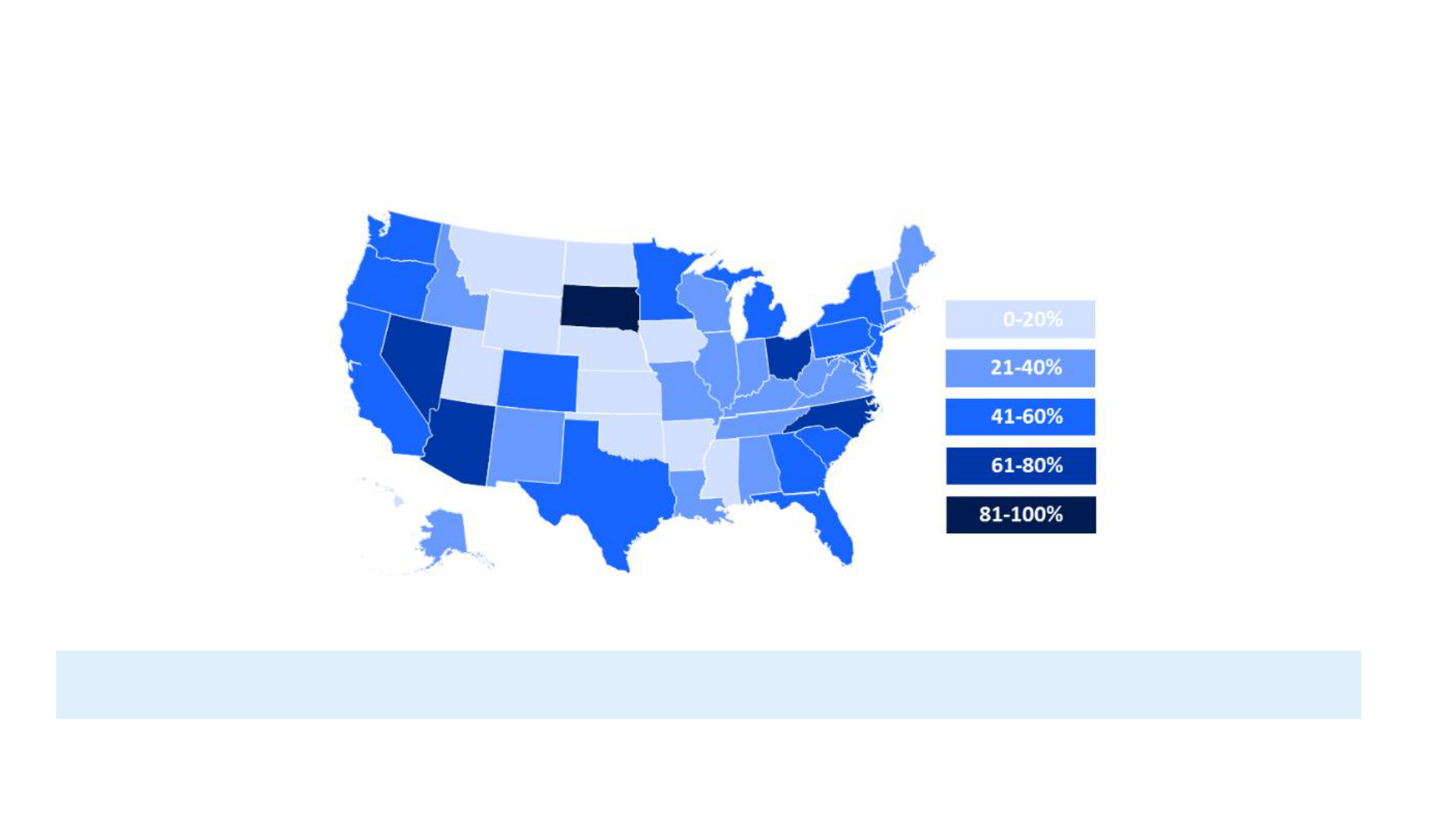
RTP Network Coverage by US Deposit Share
As of now, RTP network reaches over 56% of U.S. transaction accounts, and is on path to reach nearly all U.S. accounts by end of 2020. Zelle is the
preferred network for individual payments as it allows use of aliases. Currently, Zelle uses legacy ACH-next day settlement model. With the integration of Zelle
with RTP for the settlement service, P2P payments initiated through Zelle will also be processed using RTP network.
Note: Adoption statistics are confidential and not published by TCH
Source: TCH website
26
World Bank Fast Payments Toolkit
4. Technical Details and Payment Process
Chapter Summary:
• RTP system is based on ISO 20022 standard as it allows global interoperability, rich
remittance data, uniform and reusable messages and paves way for system as a strategic
platform for innovation
• As a core payment infrastructure, RTP can support QR payments. Currently, no financial
institutions and payment service providers are using RTP system for QR payments
• APIs have not been enabled by TCH for RTP system. Participants are providing APIs to end
customers for transaction instructions as well as value added services
• TCH has mandated use of multi factor authentication for all RTP payments. These
standards comply with the strong customer authentication standards
• RTP does not require one-time customer registration. Any account at a participating FI can
receive RTP credit transfers without registration. The payment process includes payer-
payee transaction fulfilment and inter-participant settlement
• RTP uses real time gross settlement mechanism for final settlement between the
participants as it allows instant settlement finality
Chapter sections:
4.1. Technical Details | Messaging Format and QR
Codes
4.1. Technical Details | APIs and Customer
Authentication
4.2. Payment Process (Customer Registration,
Transaction Fulfilment, Liquidity Management and
Settlement)
Source: TCH | Primary Interviews
27
World Bank Fast Payments Toolkit
4.1. Technical Details | Messaging Format and QR Code
Messaging Format
• ISO 20022 was chosen as messaging standard as it enables rich and
consistent follow of information. FIs can embrace this information to build
new and innovative products by embedding extensive information not
available in current payment messages into RTP payment messages
• The quantity and quality of data carried in ISO 20022 messages can be
extended to include remittance notes and additional supplementary
information which reduces the need for custom development in specific
geographic markets or industries to deliver to specific client needs
• Further, the use of the ISO 20022 standard enables multinational FIs and
corporates to utilize one message standard across all payment related
activities
• While RTP is a domestic payment system, use of ISO 20022 positions the
system to support cross-border commerce and interoperability with
other schemes as real time payments evolve in the global marketplace
ISO 20022
QR Code
Not supported, though system has technical capability
to support QR payments
• RTP has been developed as a core payment system. It is not involved in
development of end user application. Financial institutions and third-
party payment service providers are responsible for developing the
applications for the end users
• Technically RTP can support payments through QR codes, though currently
are currently no third-party application which is using the RTP network
for QR payments
• The US Faster Payments Council has a working group, which is looking at
the possibility of enabling QR payments using real time payments, including
the RTP network
RTP has adopted ISO 20022 messaging standard for allowing rich flow of information. Currently RTP is not being used for QR payments though a working
group of the US Faster Payments Council is looking at possibility of enabling QR payments using real time payments
Source: TCH | Primary Interviews
28
World Bank Fast Payments Toolkit
Customer Authentication
• According to the RTP Operating Rules, participants are mandated to establish
multifactor authentication (something you know and something you have
or something you are) to authenticate the identity of customers
• The TCH RTP system is open and flexible and supports various authentication
methods depending on customer segment or channel used to initiate the
transaction
• Participants are also obligated implement a layered security program that
includes fraud detection and monitoring as well as other effective controls
Multi factor authentication
APIs
• APIs are not enabled by TCH for the RTP system as participants connect
using ISO 20022 messages with the system
• Establishing connection through ISO 20022 messages has been purposeful
due to rich nature of information provided by these standards and helps FIs
in developing products for end customers. While API based connection would
have limited this information flow
• Many financial institutions offer APIs to their end customers for transaction
instructions as well as other value-added services such as checking
transaction status, fetching transaction details, etc.
APIs provided by participants
TCH doesn’t issue any APIs for the RTP system to the participants, though participants enables APIs for their end customers. TCH has mandated use of multi
factor authentication for RTP payments
4.1. Technical Details | APIs and Customer Authentication
Source: TCH | Primary Interviews
29
World Bank Fast Payments Toolkit
Real time settlement
Transaction Basis
One-time
4.2. Payment Process
1
• Customer registration
• Creation of alias (if
applicable)
Customer
Registration
Transaction
Fulfilment
• Approach for settlement
and liquidity management
Inter-Participant
(PSP) Settlement
2
3
• Transaction Flow
• Connectivity between
participants
RTP does not require one-time customer registration. Any account at a participating FI can receive RTP credit transfers without registration. The steps in the
payment process include payer-payee transaction fulfilment and inter-participant settlement
30
World Bank Fast Payments Toolkit
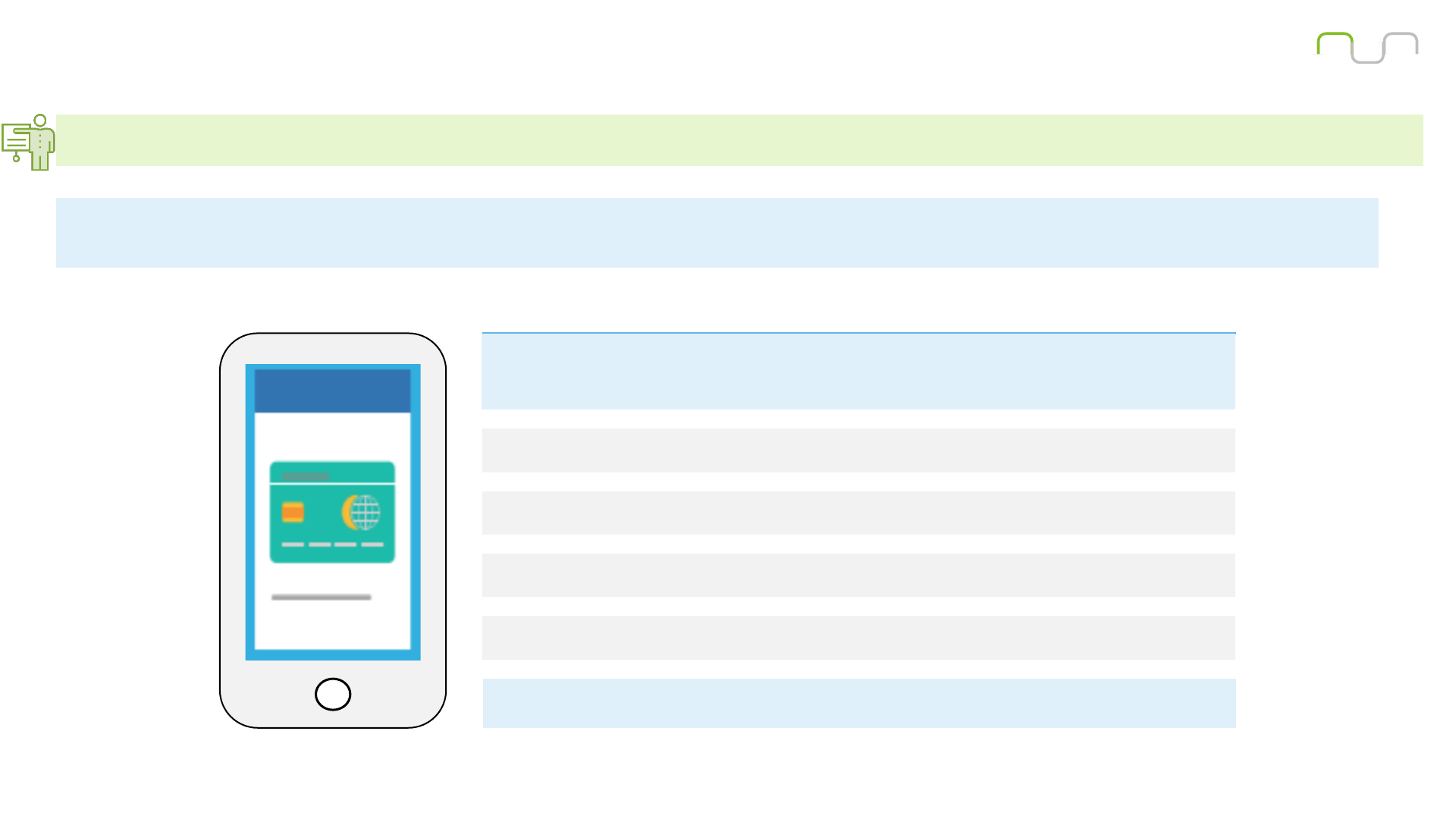
4.2. Payment Process | Customer Registration
Participating financial institutions are required to establish customer onboarding process in RTP system. Typical process for customer registration has been
described below
• RTP system is the core payment infrastructure to facilitate real-time payments. It is not involved in development of end user applications. TCH does not
prescribe any onboarding process. Only onboarding requirements relate to senders of Requests for Payments. Customers can make RTP
payments through existing channels like internet banking and mobile banking.
Source: HSBC Bank
RTP does not require a customer onboarding process however participant FIs can
establish onboarding procedure for a specific service. Onboarding process for one of
the participant FIs has been described below:
Step 1: Customer downloads the mobile banking application
Step 3: Customer registers using the Social Security Number (or Tax ID), an existing ATM,
credit or debit card number, and associated PIN
Step 4: Bank verifies the details and send a confirmation message to the customer
To make a real-time payment, customers log on to mobile banking application or internet
banking with biometrics or through digital or physical security device
Step 2: Customer requests for new registration through the application
31
World Bank Fast Payments Toolkit
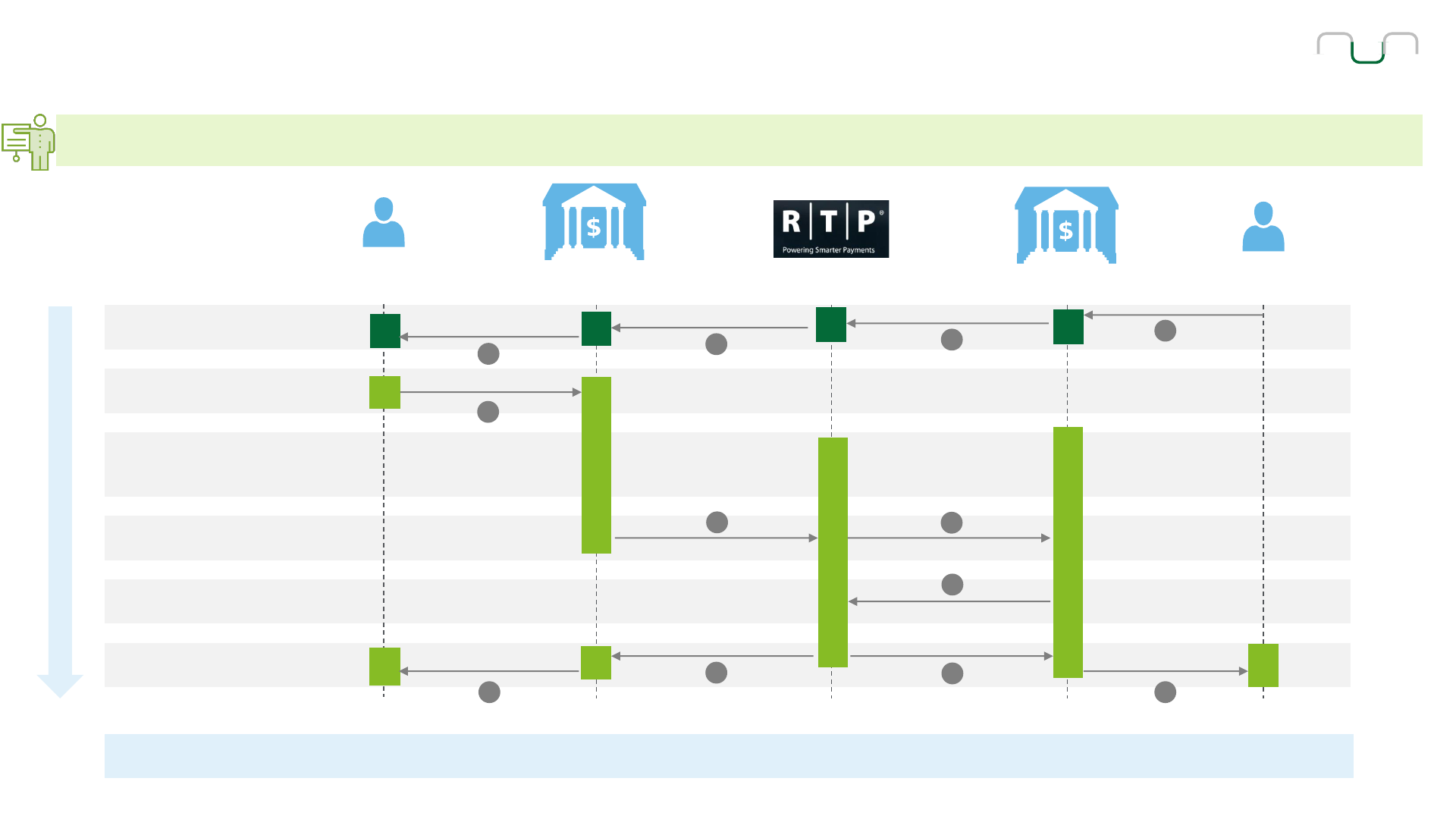
4.2. Payment Process | Transaction Fulfilment | Illustrative for Request for Payment
Typical transaction fulfilment process which is followed for Request for Payment with Credit Transfer has been described below. Intra-bank transfer are
not supported in RTP system
Payer
Payer FI
Payee FI
Payee
Request for Payment
Initiation
Authentication
Payer Authorization
Payer’s FI Approval
Clearing
Receipt and Settlement
Reconciliation
1
2
3
4
5
6
7
8
9
9
10 10
Payment Request
Message
Request for PaymentRequest for Payment
Notification of
Request for Payment
Payment initiated
(channel specific)
Credit transfer
(pacs.008)
Credit transfer
(pacs.008)
Accept/Reject
(pacs.002)
Accept/Reject
(pacs.002)
Accept/Reject
(pacs.002)
Confirmation
(email, text, etc.)
Confirmation
(email, text, etc.)
The payment request message is delivered in real time by the RTP core infrastructure; however, the payer determines when to initiate a credit transfer in
response to the request for payment.
Time
0 sec
1 sec
2 sec
3 sec
5 sec
1 sec
Source: RTP Playbooks
32
World Bank Fast Payments Toolkit
4.2. Payment Process | Liquidity Management and Settlement
Final settlement in RTP is done through Real-time Gross Settlement (RTGS) mechanism. This mechanism was used with a prefunding model to enable the
immediate finality of payments without settlement risks
Approach
Real time Not applicable
RTGS
Settlement Mechanism
• Settlement in RTP system is done through Real-time Gross Settlement mechanism through a fully prefunded account, jointly owned by all the financial institutions
in the Federal Reserve. The use of a prefunded model to achieve real time settlement eliminates the settlement risk and enables immediate finality of all payments
• In 2017, Federal Reserve published regulations for creation of Joint Federal Reserve account that can be owned by multiple FIs. This joint account allows financial
institution to pool their funds and facilitate innovative payment services. RTP system uses similar joint prefunded balance account for fulfilling settlement obligations
of the participants
• The RTP system clears and settles payments on a good funds model. The RTP system verifies and reserves settlement capacity by the sending participant before
forwarding the payment to the receiving participant, eliminating the risk of settlement failure. In case the sending participant has an insufficient prefunded position
to cover a payment, the core infrastructure will reject the payment. Overdrafts or negative prefunded positions are also not permitted in the RTP system
• TCH has established a prefunded requirement for each sending participant, which must be funded and maintained by the financial institution to send payments.
Financial institutions that do not fund for themselves must have an arrangement in place with another financial institutions for fulfilling funding obligations
• RTP system continuously records net position and current prefunded position. In case of successful transfer, system records entries by decreasing net position
and current prefunded position of sending participants or funding provider, and increases net position and current prefunded position of receiving participants or its
funding provider
• Participants provide funding through Fedwire payments to the joint account. Prior to the close of Fedwire, financial institutions must ensure that there is sufficient
prefunding in place to fund the net amount of transactions until Fedwire reopens on the next business day
• If a Payment Message is cancelled, no changes are made to the Net Position or Current Prefunded Position of the Receiving Participant or the Current
Prefunded Position of the Funding Provider
• Settlement with respect to a Payment Message is complete when the RTP System has recorded both the decrease in the Sending Participant's Net Position and the
increase in the Receiving Participant’s Net Position in the joint federal reserve account
Type | Time
Source: TCH | Primary Interviews
33
World Bank Fast Payments Toolkit
5. Governance Framework
Chapter Summary:
• The legal framework supporting RTP activities is comprised of comprised of RTP
Operating Rules and RTP Participating Rules along with existing payments laws
wherever applicable
• TCH is regulated and is regularly examined by supervisory staff from the Board of
Governors of the Federal Reserve System (FRB), Office of the Comptroller of the Currency
(OCC) and the Federal Deposit Insurance Corporation (FDIC). The Federal Reserve entity
that regulates the RTP Network directly is the Federal Reserve Bank of New York, under a
regulatory framework established by the Federal Reserve Board
• TCH has established the RTP Business Committee to govern the RTP network. It is
responsible for providing input and guidance on the strategic execution of the RTP network
• RTP Operating Rules have established multiple layer of risk mitigation for the system.
Apart from this, TCH also applies a risk management framework for ensuring security,
reliability and resiliency of the system
• Settlement risk is eliminated in RTP system by using fully pre-funded real-time settlement
• No centralized guidelines has been issued by TCH for inter-bank dispute scenarios and
customer complaints resolution. US Federal regulations (Regulation E) and State laws
(UCC 4a) govern both interbank and customer disputes. Though RTP System provides a
mechanism to participants to send and respond to requests for the return of funds
Chapter sections:
5.1. Legal and Regulatory Aspects
5.2. Risk Management
5.3. Dispute Resolution and Customer Complaints
Source: TCH | Primary Interviews
34
World Bank Fast Payments Toolkit
5.1. Legal, Regulatory and Governance Aspects (1/2)
• RTP Participation and Operating Rules act as the legal framework for the system. These RTP Operating Rules have been drafted
to define the rights and responsibilities of participants and TCH with respect to RTP
• The participation rules will address topics including, among others, general eligibility requirements; the process for connecting to
the RTP system through a third-party service provider; and requirements in the event of a change of name, form of organization, or
control of a participant
• The operating rules will address topics including, among others:
• General participant eligibility requirements and operating responsibilities
• Eligible payments
• The protection of confidential information and customer information security
• Payment notification and messaging
• Funds availability
• Errors and unauthorized transfers
• Funding and settlement
• Risk management
• Enforcement of RTP rules
• Choice of Law
• EFTA (Electronic Fund Transfer Act) Consumer Payments (For an RTP Payment any part of which is subject to the
EFTA): the rights and obligations of a Participant and end user is governed by:
• the EFTA and Regulation E, to the extent applicable to the transaction
• to the extent consistent with EFTA and Regulation E as applicable to an RTP Payment, by RTP Operating Rules, and
the laws of the State of New York, excluding Article 4-A of the New York Uniform Commercial Code
• Commercial and Non-EFTA Consumer Payments (For an RTP Payment in which no part of the transaction is subject to
the EFTA): Sending Participant, Receiving Participant and other parties involved in an RTP transaction are governed by RTP
Operating Rules and by the laws of the State of New York, including Article 4-A of the New York Uniform Commercial Code
TCH has established RTP Participation and Operating Rules to constitute the legal framework of the system. Existing laws has been also incorporated to
complete the legal basis of the system
Institutional and
Governance Framework
Legal Framework
RTP Participation and
Operating Rules along
with existing relevant
laws
Regulator
FRB, OCC and FDIC
Overseer and Operator
The Clearing House
Source: RTP Operating Rules | RTP Playbooks
35
World Bank Fast Payments Toolkit
5.1. Legal, Regulatory and Governance Aspects (2/3)
• Due to the important nature of the Clearing House’s role in the USA financial system, it is regulated and is regularly examined by
supervisory staff from the Board of Governors of the Federal Reserve System (FRB), Office of the Comptroller of the
Currency (OCC) and the Federal Deposit Insurance Corporation (FDIC)
• The Federal Reserve entity that regulates the RTP Network directly is the Federal Reserve Bank of New York, under a regulatory
framework established by the Federal Reserve Board
• Under the Bank Service Company Act, the Clearing House, and all of the payments systems it operates including the RTP
network, are subject to regulation and examination to the same extent, as if the services being provided were being performed by a
depository institution that is subject to FRB, OCC or FDIC supervision itself.
• Through an arrangement among the federal financial regulatory agencies through the Federal Financial Institutions
Examination Council, the FRB acts as the lead examiner of TCH for examinations conducted under the Bank Service Company
Act
• The Clearing House has also been designated by the Financial Stability Oversight Council as a Systemically Important Financial
Market Utility (SIFMU) under Title VIII of the Dodd-Frank Act and is subject to a regulatory and supervisory regime
• While TCH’s regulation and supervision under Title VIII relate specifically to its role as the operator of CHIPS, TCH operates as a
single entity in the operation of its payments systems and, therefore, many of the requirements of Title VIII may affect its broader
operations such as RTP system
• Federal Reserve is not actively engaged in the oversight of the RTP system. Federal Reserve and other federal agencies regulate
TCH payment systems, including the RTP network, as a Technology Service Provider. Also, there is a separate examination process
for the regulation of the CHIPS (high value payment network) as a SIFMU
• TCH has constituted RTP business committee in order to perform overseeing activities for RTP system
Federal Reserve is not actively engaged in the oversight of the RTP system. Although Federal Reserve has supervisory authority over its operator TCH
because of its operation of CHIPS that has been designated under the USA Law
Institutional and
Governance Framework
Legal Framework
RTP Participation and
Operating Rules along
with existing relevant
laws
Regulator
FRB, OCC and FDIC
Overseer and Operator
The Clearing House
Source: RTP Operating Rules | RTP Playbooks
36
World Bank Fast Payments Toolkit
5.1. Legal, Regulatory and Governance Aspects (3/3)
TCH has established RTP Business Committee to govern the RTP network. comprised of representatives from TCH owner banks and representatives from
non-member financial institutions
• The principal governance arrangements for the RTP system has been set forth in the limited liability company agreement.
Management of TCH is under the direction of two boards of directors: the Supervisory Board and the Managing Board
• According to the LLC Agreement, Supervisory Board has overall responsibility for the business of TCH, while the Managing Board,
which reports to the Supervisory Board, is responsible for oversight of TCH’s business and financial performance and for setting
TCH’s strategic agenda
• TCH has established the RTP Business Committee to govern the RTP network. It is responsible for providing input and guidance
on the strategic execution of the RTP network
• The Business Committee is also responsible for ensuring prudent risk management practices, promoting the design, operation,
and management of the system, and establishing or amending the rules for the RTP network
• The RTP Business Committee is comprised of representatives from TCH owner banks and representatives from non-member
financial institutions. The participation of non-member financial institutions ensures that non-member financial institutions have
an active voice in the governance of the RTP network
• In addition, the RTP system is also managed and supported by executives, officers, and employees of TCH, including product,
operations, technology, customer relations, risk-management, audit, and legal staff
Institutional and
Governance Framework
Legal Framework
RTP Participation and
Operating Rules along
with existing relevant
laws
Regulator
FRB, OCC and FDIC
Owner and Operator
The Clearing House
Source: RTP Operating Rules | RTP Playbooks
37
World Bank Fast Payments Toolkit
5.2. Risk Management
The RTP network has multiple layers of risk mitigation. Some key ones have been mentioned below:
• All participants are required to meet information security requirements including multi-factor authentication of
originators and data center security standards
• The RTP network is configured for multi-site, multi-node, high availability operation. The multi-site operation is
active/active for continuous operation
• All data transmissions are encrypted and require digital signatures at sign-on. All messages are encrypted and
digitally signed
• Administrative access by participants, processors and operators are subject to privilege-based access controls
secured by individual tokens
• RTP operating rules also require that sending participants employ multi-factor authentication and processes to
detect and prevent unauthorized payment initiation. The RTP network does not support debit transactions, only
credit transfers. All payments must be authorized by the sender to their financial institution
• All message exchanges are based on an assured delivery model. The receiving participant must send a confirming
message, or the transaction is cancelled. The network sends final confirming messages to both the sending and
receiving participant. The message flows are designed to ensure a “fail safe” outcome in all operational failure
scenarios.
• Participants are required to report all incidents of fraud to RTP network administration for tracking and analysis
• Based in incidents reported by participants or analysis of network activity, Network administration can request an
that a participant investigated suspicious activity on any of its accounts
• RTP network administration also monitors the operational performance of participants and processors, and will
require remediation of any situation that may adversely affect network performance or the operations of other
participants
TCH applies a risk management framework for operation of the RTP system for ensuring security, reliability and resiliency of the system. RTP Operating
Rules have also established multiple layers of risk mitigation
TCH also applies a risk management framework for operation of the RTP system. This framework exists outside of the RTP Operating Rules, and includes significant
resources devoted to system reliability and resiliency, security (e.g., physical, operational, network security), incident response, overall risk management, and
comprehensive business continuity plans
Potential Risk
Risk Controls
… are receiving participants
… support 3rd party services
… support request for payments
… both send and receive payments
Low
High
Participating FIs that…
Source: RTP Playbooks | Primary interviews
38
World Bank Fast Payments Toolkit
5.2. Risk Management
Credit and
Liquidity
Risks
• TCH has a sole discretion to determine the prefunding requirement for:
• Sending participant that is a funding participant in the system
• Sending participant that is a non-funding participant but has a current prefunded position (participants with a funding obligation)
• Each Funding Provider
• During Fedwire operating hours, participant with funding obligations and funding providers are required to monitor their current prefunded position
and provide supplemental funding to the Prefunded Balance Account if current prefunded position falls below their prefunded requirements
• Supplemental funding for maintaining current prefunded position based on prefunded requirement should occur:
• No later than the next opening of Fedwire, if the current Prefunded Position falls below the Prefunded Requirement during hours when Fedwire
Funds is closed
• Before the next close of Fedwire, if the Current Prefunded Position falls below the Prefunded Requirement during hours when Fedwire is open
• During Non-Fedwire hours, supplemental funding is provided in advance of the close of Fedwire to ensure that the funding provider or participant’s
current prefunded position is sufficient to cover its anticipated payment origination activity when Fedwire is closed
• Funding providers and participants with funding obligations can also have arrangements with each other to transfer liquidity through RTP Payments
in case their current prefunded position becomes low during Non-Fedwire hours. Such liquidity transfers must be reported to TCH within ten banking
days using procedures specified by TCH
Settlement risk is eliminated in RTP system by using fully pre-funded real-time settlement. TCH has established several guidelines for participants for
maintaining their pre-determined pre-funded positions. TCH has also issued guidelines for mitigating fraud risks
Fraud
Risks
• TCH has established a tiered approach to fraud prevention and mitigation as not all financial institutions participate in real-time payments at the same
level
• All participating financial institutions are required to:
• Comply with Federal Financial Institutions Examination Council (FFIEC) guidelines as applied through prudential regulator examination
• Report fraudulent behavior to The Clearing House and/or sending financial institutions
• React to alerts from centralized activity monitoring utility
• Apart from these, there are additional compliance requirements for FIs that support request for payments and permit third party payments
• In addition to the centralized fraud monitoring, TCH has ability to limit the RTP activities of participating FIs that violate system rules and risk
management requirements
Source: RTP Operating Rules | RTP Playbooks
39
World Bank Fast Payments Toolkit
5.2.1. Cyber Resilience and Data Management
Data
Manange-
ment
•
RTP Operating Rules include provisions regarding the treatment of confidential information by TCH and participating FIs including encryption
requirements for the storage and transmission of RTP message data
•
Participating FIs holding customers’ accounts are subject to existing consumer privacy laws regarding the proper use of consumer data and
restrictions on disclosure of such information to third parties. Participating FIs are subject to the Gramm-Leach-Bliley Act, which governs the
treatment of nonpublic personal information about consumers by financial institutions and requires financial institutions to safeguard the security and
confidentiality of customer information
•
Additionally, the PSP compliance criteria require PSPs that access the RTP system through banks to develop and implement administrative, technical,
and physical safeguards to protect the security, confidentiality, and integrity of customer information, as well as to ensure the proper disposal of
customer information
Cyber
Resilience
• TCH monitors its system and its procedures for security breaches, violations, and suspicious activity, including suspicious external activity
(unauthorized probes, scans, or break-in attempts) and suspicious internal activity (unauthorized system administrator access, unauthorized changes to
its system or network, system or network misuse, or theft or mishandling of customer information)
• Industry-standard information channels are monitored by TCH for newly identified system vulnerabilities regarding the technologies and services
(including application software, databases, servers, firewalls, routers and switches, hubs, etc.) and fix or patch any identified security problem as soon
as commercially reasonable, based on TCH’s determination of the severity level of the security problem
• TCH maintains and implements appropriate plans to assure its continued operation. These plans shall include the following: recovery strategy,
documented recovery plans covering all areas of operations necessary to delivering services as required by the RTP Operating Rules, vital records
protection, and testing plans
• The plans shall provide for backup of critical data files, customer information, application software, documentation, forms and supplies. The recovery
strategy shall provide for recovery after both short- and long-term disruptions in facilities, environmental support, and data processing equipment
• TCH shall continue to provide service to a participant if the participant activates its contingency plan or moves to an interim site to conduct its business,
including during tests of the Participant’s contingency operations plans
• TCH’s contingency plans for disruptions in facilities, environmental support, and data processing equipment provides the ability to bring any impacted
operations that are necessary to delivering services as required by the RTP Operating Rules up to full capacity at its back-up site within 60 minutes of
a declared disaster
As per the RTP Operating Rules and RTP Customer Information Security Standards and Requirements, TCH has established guiding principles for
ensuring the cyber resilience and data privacy. It has also obligated participants to follow certain guidelines for safeguarding the sensitive information
Source: RTP Operating Rules | RTP Playbooks
40
World Bank Fast Payments Toolkit
5.3. Dispute Resolution and Customer Complaints
Customer complaintsInter-bank Dispute Resolution
• RTP Operating Rules incorporate existing laws (i.e., EFTA, Regulation E
and UCC 4A) that sets forth a well-established framework regarding banks’
liability for unauthorized transactions from their customers’ accounts, as well
as specific requirements regarding the resolution of errors from consumer
accounts
• This structure simplifies the account-holding financial institution’s dispute
investigation processes and minimize the need for a detailed set of
interbank dispute resolution rule
• RTP System provides a mechanism to participants to send and respond to
requests for the return of funds for any reason, including unauthorized or
erroneous RTP Payments
• TCH shall not be a party to any dispute between Participants regarding
liability for erroneous or unauthorized RTP Payments. Such determination is
left to the participants, including through any available dispute resolution
and/or judicial process
• TCH shall only be liable for RTP Payments if such RTP Payments are
unauthorized and the RTP Payments were caused by dishonest or
fraudulent acts of TCH or its representatives
• There are no centralized guidelines for resolution of customer complaints
• Though RTP Operating Rules obligates the sending financial institutions to
put in place policies and procedures for handling customer claims for
unauthorized transfers and funds sent in error
• Disputes and exception scenarios are addressed by additional messages
such as request for information and request for return of funds.
Currently, number of disputes and exception scenarios are low in RTP
• Receiving FIs must have policies and procedures to respond to requests to
reclaim funds sent in error
No centralized guidelines has been issued by TCH for inter-bank dispute scenarios and customer complaints resolution. Though RTP System provides a
mechanism to participants to send and respond to requests for the return of funds
Source: TCH | RTP Operating Rules
41
World Bank Fast Payments Toolkit
6. Annexure
Chapter sections:
6.1. Key Features

42
World Bank Fast Payments Toolkit
Features
Key Highlights
Payment Types & Use Cases/Services
Settlement
Approach
Type | Time
Hub
RTGS
Distributed
clearing
Individual Business Government
Merchant
Payments
Bulk / Batch
Payment
Request to Pay
Bill payments
Recurring
payments
Cross-border
payments
Source: The ClearingHouse | ACI Report | FIS Report
Operating hours
• 24*7 including weekends and bank holidays
Payment Speed
• Real time
Transaction limit
• $100,000
Alias
• No aliases supported by the core infrastructure
Channel
• Branch, ATM, Internet banking and Mobile banking
User Charges
• At participants’ discretion to charge customers for
RTP payments
Infrastructure Setup
• New system
Messaging format
• ISO 20022
Use of Open APIs
• Open APIs not available
Authentication
• Multifactor authentication
Real time Not applicable
6.1. Key Features

